Wallabag + CapRover in 5m
Wallabag “is a self hostable application for saving web pages”
CapRover “is an extremely easy to use app/database deployment & web server manager”
This is a quick and dirty setup for testing Wallabag (without full database or redis, or email, etc).
5m setup
- Setup new app with persistent data enabled in CapRover
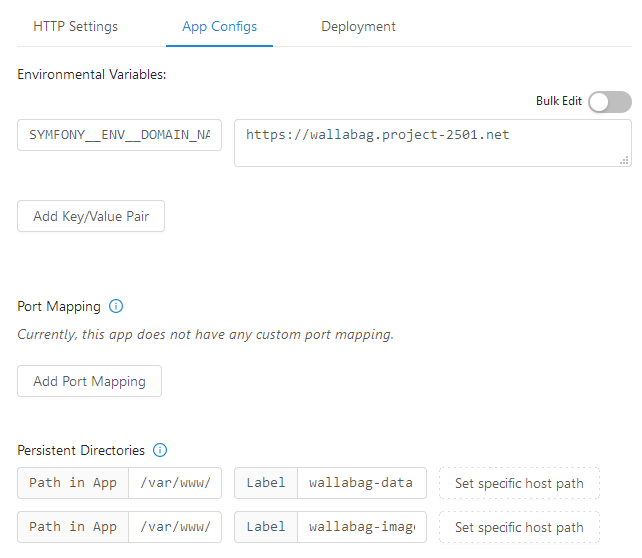
- In App Configs add the environmental variable
SYMFONY__ENV__DOMAIN_NAMEand set it to the full URL of where you want Wallabag. e.g.https://wallabag.rover.example.com - Add two persistent directories ofr
/var/www/wallabag/data/and/var/www/wallabag/web/assets/images/ - In the deployment tab scroll down to method 4 and enter:
FROM wallabag/wallabagand deploy - In 30s Wallabag should be available at
https://wallabag.rover.example.com - Default login is
wallabag / wallabagso you probably want to go change that
Example App Configs
Issues
- No CSS or images: Need to make sure
SYMFONY__ENV__DOMAIN_NAMEpoints to the full URL including protocol. e.g.https://wallabag.rover.example.com - 502 error: Log into to server and check Docket logs. e.g. `
docker service logs srv-captain--wallabag --followordocker service ps srv-captain--wallabag --no-trunc

